About Us
Run and owned by Australians, our Australian staff based exclusively in Sydney have over 35 years of IT experience starting in the mid-1980s in both the private and government sectors. We have seen massive changes in Infrastructure over time and have constantly adapted to meet the challenges of ever-evolving software and hardware..
- The Linux posix-compliant operating system is the safest in the world
- Storage is now very fast and very secure. You can now have your own cloud storage service.
- Backup tools have evolved quickly over time to meet ever-expanding data storage
- Network speeds can now cater for higher data and larger rates
Why do we offer these build and maintenance services?
We have all heard about the CYBER-ATTACKS on multi-national and security companies, governments and others. Businesses are losing their clientele as their data is no longer safe from any actor that wishes to gain access to secure data. Unexpected data loss from hard drive failures, natural disasters, and ransomware attacks pose potential threats to your precious data. You need extra protection in case your IT equipment is affected by the above, crashes or gets infected by ransomware. For business users, it is recommended to follow a restricted and encrypted access local copy and off-site strategy to make sure that all your core business data and critical information are always secure.Remember, data backup is the only way to recover from Ransomware without paying the ransom.
Services
-------------------
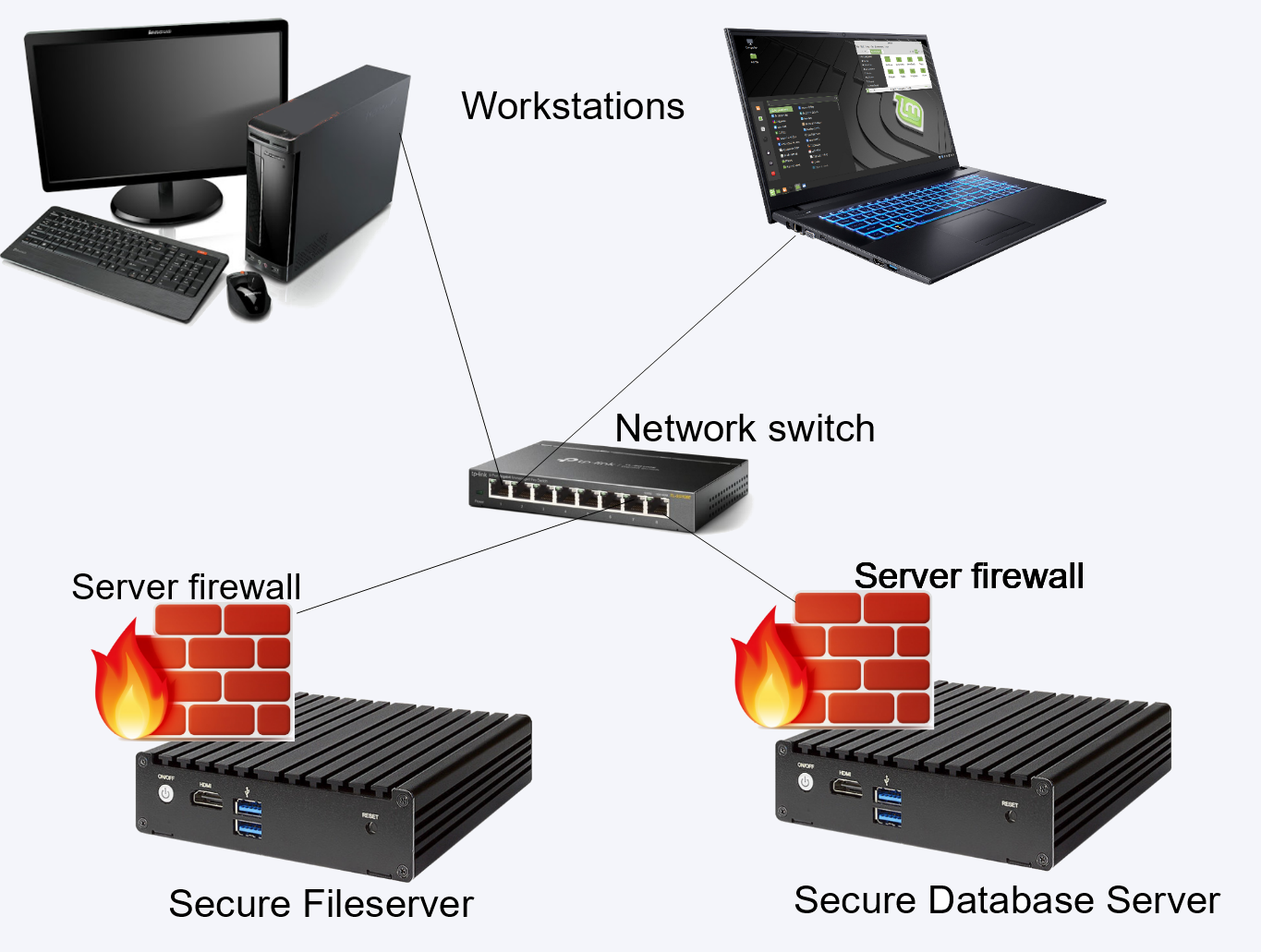
Whether it's a build and/or a maintenance solution you need, the four skills represented below bundle into a turnkey solution. Together they form a powerful combination to ensure your precious data is kept safe and secure.
Linux Servers
The Linux operating system can be secured behind it's own firewall. This makes it very hard for hackers to do their thing. Intrusion detection is standard. All operations are transparent to the customer.
Backups
All your files are backed up on a nightly basis or more frequently if required. Restoring data will be in your hands; you have control.
Online Storage
All your files are kept locally on encrypted drives; as much as you need. Bear in mind, the data you store is ONLINE. Cloud offerings are offline unless there is an expensive app to supply it, therefore you need to download files, work on them and send them back to the cloud for storing again. You will see your files in a directory on your PC or laptop only by logging in for your security.
Disaster Recovery
Data is replicated offsite so there is nothing to worry about in case of a disaster. Your data will remain safe.
Maintenance Pricing
Any maintenance contract's payment structure will be one that works for you. A combination of fixed-fee and variable payments works well for most maintenance contracts. We use a fixed-fee payment model for routine, on-duty maintenance and a variable payment model for both on-duty and after-hours urgent and emergency trouble calls.
- Customer Portal
- 24x7 Service Desk
- Standard SLA Support
- Technical Account Management
- Maintenance and Alerts
- Real-time reporting
- 24x7 Infrastructure monitoring
- Annual requirements review
Our support plans provide for:
Linux Server Plans
$30starting at per month
- File servers
- Database servers
- Internal webservers
- Graphic design
- Audio/video editing
- Streaming
Server and Storage Plans
$80starting at per month
- Online data files
- Disaster recovery
- Backups and restores
- Fast access file retrieval
- Real-time viewable status
- Encrypted status
Turnkey Solution Plans
$200starting at per month
- Server and storage network
- Applications access
- Reliability trending reports
- Capacity management reviews
- Daily system updates
- Online reporting
Frequently Asked Questions
We are not a multi-national company where service is second to profit. We are a small, fully-Australian owned and run service where your IT needs are met with that personal touch.
-
Attacks in the cloud? What attacks?
Our services provide secure and safe data, storage and server management as opposed to a cloud solution that nobody can claim to be 100% safe. There can be technical outages/downtime that can lead to temporary suspension of business process and if internet connection is offline, accessing applications, server and data from the cloud is not possible. With the cloud, your storage is also NOT online without a 3rd party application. It needs to be downloaded first and only then can it be accessed directly.
There are DOZENS of cyberattacks PER MONTH on companies that are cloud-attached. Only a few are listed below.
The Globe (Crowdstrike on Microsoft) - July 2024
Impact: An estimated 8.5 million computers were disabled during the worldwide outage.
Royal Mail - January 2024
Impact: Royal Mail has asked people to stop sending mail abroad due to a "cyber incident" causing severe disruption.
Optus - September 2023
Impact: Telco admits almost 10 million current and former customers’ data, ie dates of birth, passport and driver's licence numbers and addresses had been accessed. 10,000 records released. Optus hit with class action lawsuit.
United Kingdom's National Health Service (NHS) - August 2023
Impact: 111 emergency services, ie 85% of NHS services down.
Kaseya supply chain ransomware attack - July 2022
Impact: Via Solarwinds - 1,500 companies were affected.
RockYou2021 - July 2022
Impact: 32 million user passwords leaked.
Facebook - April 2022
Impact: Personal data of 530 million users. Facebook has no plans to notify any of them
SITA - Airline IT provider - February 2021
Impact: Personal data of 400 airline customers for Star Alliance and OneWorld members, eg Singapore Airlines, Air New Zealand, Lufthansa, Malaysia Airlines, Finnair, Japan Airlines and Cathay Pacific. SITA have refused to comment on the extent
Cybersecurity firm FireEye, US Treasury, Microsoft, Intel, MasterCard, Lockheed Martin and PricewaterhouseCoopers; approximately 18,000 companies compromised - December 2020
Impact: The extent of the damage is unknown
Instagram - August 2020
Impact: 96 million records - exposed real name, photo, gender, age, location, likes
TikTok - August 2020
Impact: 42 million records - exposed real name, photo, gender, age, location, likes
Youtube - August 2020
Impact: 4 million records - exposed real name, photo, gender, age, location, likes
Facebook - April 2020
Impact: 267 Million Facebook users - identities stolen
Zoom - April 2020
Impact: 500,000 accounts - email address, password, personal meeting URLs for sale
Sina Weibo - March 2020
Impact: 538 million accounts - real names, site usernames, gender, location, and phone numbers had been posted for sale on dark web markets
-
How do we prioritise emergency situations and response times?
Depending on maintenance service requirements, prioritize after-hours trouble calls as routine, urgent or emergency, and set respond-by times for urgent and emergency maintenance calls. For example, categorize malfunctioning air conditioning as urgent, and require on-call maintenance personnel to be on site and working on the repair within two hours.
-
What is our payment model?
Any maintenance contract's payment structure will be one that works for you. A combination of fixed-fee and variable payments works well for most maintenance contracts. We use a fixed-fee payment model for routine, on-duty maintenance and a variable payment model for both on-duty and after-hours urgent and emergency trouble calls. For example, increase a fixed fee payment by 10 percent for urgent after-hours calls and 20 percent for emergency calls. Include a reimbursement model if you plan to reimburse the contractor for all or a percentage of the tools and supplies he provides.
-
How do we know that our system is running ok?
We frequently monitor and collect data down to the hour for trending load, predictive failures and performance impacts to ensure reliability and trust. Your business can receive our monitoring reports on a daily basis if you require.
-
How does the at call maintenance contract work?
This is a 24 x 7 365 days a year on-call requirement by the business that we provide for your software and hardware according to the degree of urgency. Outcome-based requirements are especially important if you are requiring facilities or equipment maintenance services for any shortfall in in-house knowledge, technical skills or the tools and supplies required to perform maintenance or repair work.